Product Store
73 resources available · members get 20% off everything
⚡ Get 20% off everything — from $8/month

SSH Pentesting Playbook
Your complete field guide to SSH security assessment — enumeration, brute-forcing, key attacks, tunneling abuse, and post-exploitation pivoting.
Wfuzz Field Guide
The definitive Wfuzz reference for bug bounty hunters and pentesters — every option, filter, and payload type explained with real-world attack examples.
Firefox Pentesting Add-ons
Hand-picked Firefox extensions every web application pentester needs — proxy setup, header analysis, cookie editing, and recon automation all in one guide.
DNS & DHCP Pentesting Playbook
Deep-dive into DNS and DHCP attack techniques — zone transfers, DNS spoofing, DHCP starvation, and rogue server attacks with step-by-step examples.

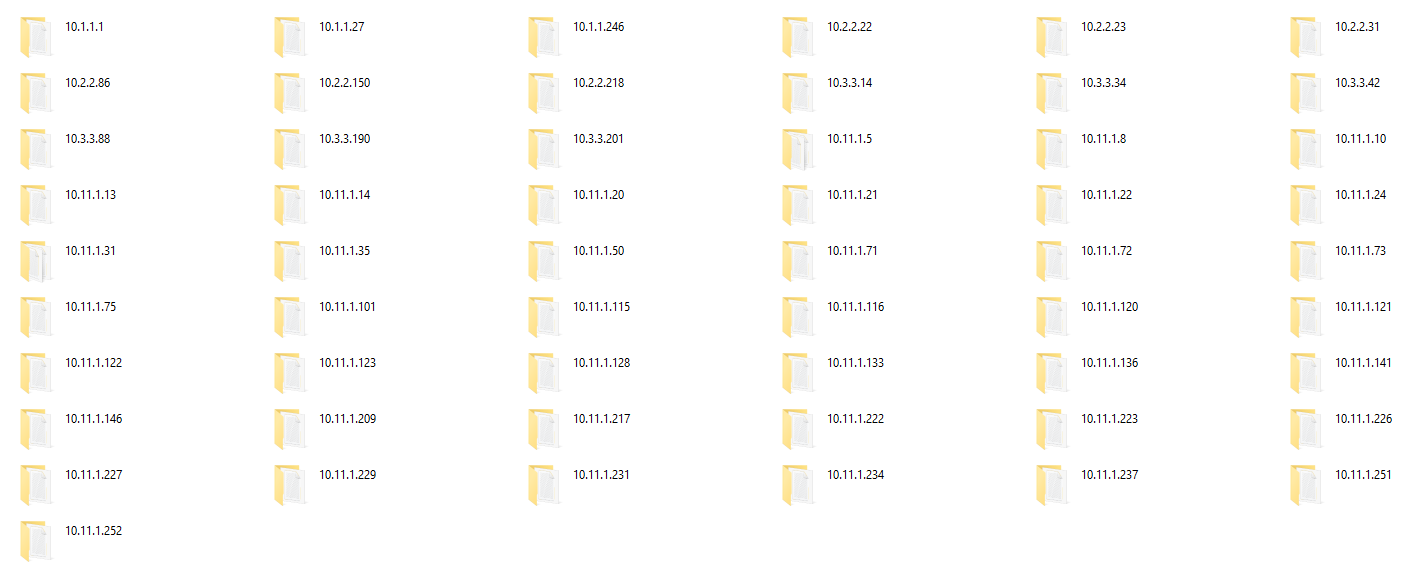
HTB OSCP-Like Labs
Curated HackTheBox machines that closely mirror the OSCP exam — sorted by difficulty with methodology notes for both Windows and Linux targets.
WordPress Exploitation Playbook
The attacker's guide to WordPress — plugin enumeration, theme exploitation, credential attacks, XML-RPC abuse, and full admin-to-shell walkthroughs.
PEN-200: Penetration Testing with Kali Linux (OSCP)
The official OffSec PEN-200 course — complete OSCP exam preparation covering buffer overflows, Active Directory, web attacks, privilege escalation, and the Try Harder mindset.
WEB-300: Advanced Web Attacks and Exploitation (OSWE)
Official OffSec WEB-300 course for OSWE certification — master white-box web application testing, source code review, authentication bypass, and custom exploit development.
Hacking Books Bundle
Curated bundle of top hacking and security books — covers offensive security, network attacks, web exploitation, malware analysis, and red team operations.
Hands-On Hacking
A hands-on introduction to ethical hacking — network scanning, vulnerability assessment, exploitation, and post-exploitation with real lab exercises throughout.
Real-World Bug Bounty
Battle-tested bug bounty techniques used against real programs — SQLi, SSRF, IDOR, XXE, business logic flaws, and how to write reports that get paid.
Linux Basics for Hackers
From terminal basics to full privilege escalation — everything a hacker needs to know about Linux, including file permissions, scripting, SUID/GUID, and cron abuse.

PEN-210: Foundational Wireless Network Attacks (OSWP)
Official OffSec PEN-210 course for OSWP certification — attack 802.11 wireless networks including WEP/WPA/WPA2 cracking, evil twin APs, and rogue access point deployment.

PEN-300: Evasion Techniques and Breaching Defenses (OSEP)
Official OffSec PEN-300 course for OSEP certification — master AV/EDR evasion, process injection, C2 frameworks, Active Directory persistence, and advanced lateral movement.

HTB - Active Directory Penetration Tester Path 2024
HackTheBox Active Directory Penetration Tester learning path — full 2024 edition covering AD enumeration, Kerberos attacks, lateral movement, and domain compromise.

HTB - Bug Bounty Hunter Path 2024
HackTheBox Bug Bounty Hunter learning path — 2024 edition covering web vulnerabilities, recon, and submission methodology for real bug bounty programs.

HTB - Penetration Tester Path 2024
HackTheBox Penetration Tester learning path — complete 2024 edition from fundamentals to advanced exploitation, network attacks, and reporting.

HTB - Senior Web Penetration Tester 2024
HackTheBox Senior Web Penetration Tester path — advanced 2024 edition covering complex web vulnerabilities, API attacks, and chained exploitation.

HTB - SOC Analyst Path 2024
HackTheBox SOC Analyst learning path — 2024 edition covering threat detection, SIEM, log analysis, incident response, and blue team operations.
OSCP Solutions Guide
Complete OSCP solutions and walkthrough guide — methodology breakdowns, exploitation techniques, and exam strategy from successful OSCP candidates.
OSCP PDF — Penetration Testing with Kali Linux
The official OSCP PDF study guide — complete penetration testing methodology, techniques, and exercises from OffSec.

Certified Google Red Team Specialist (CGRTS)
Complete CGRTS course material — red team operations against Google Cloud environments, GCP attack surface, and privilege escalation techniques.

CCSE — Check Point Certified Security Expert
Complete CCSE course material — Check Point firewall management, VPN configuration, ClusterXL, advanced threat prevention, and security policy.
AWS Penetration Testing with Kali Linux
Hands-on AWS penetration testing using Kali Linux — IAM misconfigurations, S3 bucket attacks, EC2 exploitation, Lambda abuse, and full cloud kill chains.
AWS Penetration Testing — Beginner's Guide to Hacking
Beginner-friendly AWS hacking guide — setting up your attack environment, IAM enumeration, S3 misconfigurations, and cloud privilege escalation step by step.
Active Directory — The Hacker's Guide
Complete Active Directory attack guide — enumeration, Kerberoasting, AS-REP roasting, Pass-the-Hash, DCSync, BloodHound, and domain persistence techniques.
Attacking Network Protocols
A hacker's guide to network protocol capture, analysis, and exploitation — ARP, DNS, SMB, HTTP, and custom protocol reverse engineering with Wireshark and Scapy.
Black Hat Go — Go Programming for Hackers and Pentesters
Build offensive security tools in Go — port scanners, packet sniffers, exploits, C2 frameworks, and network proxies written from scratch in Go.
Black Hat GraphQL — Attacking Next Generation APIs
Complete guide to GraphQL security — introspection attacks, batching attacks, injection, authorization bypass, and DoS techniques against GraphQL endpoints.
Black Hat Python — Python Programming for Hackers and Pentesters
Build hacking tools in Python — network sniffers, trojans, fuzzers, C2 channels, web scrapers, and offensive automation scripts.
Breaking into Information Security
Career guide for breaking into cybersecurity — certifications roadmap, skill development, resume tips, interview prep, and real-world career paths.
Bug Bounty Bootcamp
Complete bug bounty training from zero to first payout — recon methodology, XSS, SSRF, IDOR, SQLi, business logic, and writing reports that get accepted.
Building & Automating Penetration Testing Labs in the Cloud
Build your own cloud-based pentest lab — AWS/Azure/GCP vulnerable environments, automated provisioning with Terraform, and lab maintenance for practice.
Ethical Hacking — A Hands-on Introduction to Breaking In
Practical introduction to ethical hacking — network scanning, vulnerability exploitation, web attacks, social engineering, and the legal framework of penetration testing.
Evading EDR — The Definitive Guide to Defeating Endpoint Detection
Complete EDR evasion guide — understanding detection engines, AMSI bypass, ETW patching, process injection, custom shellcode, and behavioral analysis evasion.
Extreme Privacy — What It Takes to Disappear
Complete digital privacy guide — removing your online presence, anonymous communications, secure devices, private travel, and protecting your identity from stalkers and surveillance.
Gray Hat Hacking — The Ethical Hacker's Handbook (6th Edition)
Comprehensive ethical hacking reference — network attacks, vulnerability research, exploit development, reverse engineering, IoT hacking, and mobile security.
Hack & Leak
Real-world hacking and data exfiltration case studies — how major breaches happened, techniques used, and lessons for both attackers and defenders.
Hack The World with OSINT
Complete OSINT field guide — social media intelligence, email tracing, geolocation, phone number lookup, dark web research, and automating reconnaissance.
Hacking APIs — Breaking Web Application Programming Interfaces
Complete API security testing guide — REST/GraphQL/SOAP attacks, authentication bypass, mass assignment, BOLA, rate limiting bypass, and API fuzzing.
Hacking Kubernetes
Kubernetes security from an attacker's perspective — RBAC misconfigurations, container escapes, service account abuse, network policy bypass, and cluster takeover.
Hands-On AWS Penetration Testing
Practical AWS penetration testing with real lab exercises — IAM, EC2, S3, Lambda, RDS, and container service attacks with full exploit chains.
How to Hack Like a Ghost
Advanced operational security for hackers — anonymous infrastructure, traffic obfuscation, attribution avoidance, and staying undetected during red team engagements.
HTTP — The Definitive Guide
Complete HTTP reference for web security professionals — HTTP/1.1, HTTP/2, headers, caching, cookies, authentication, and protocol-level attack surface.
JavaScript for Hackers
JavaScript exploitation for security researchers — XSS payload crafting, DOM attacks, prototype pollution, browser exploitation, and Node.js security issues.
Metasploit — The Penetration Tester's Guide (2nd Edition)
Complete Metasploit Framework guide — modules, meterpreter, post-exploitation, pivoting, auxiliary scanners, and building custom exploits and payloads.
Network Basics for Hackers
Networking fundamentals from a hacker's perspective — TCP/IP, routing, switching, firewalls, VLANs, and how to attack and break each layer.
OSINT Techniques — 10th Edition (2023)
The most comprehensive OSINT resource — 600+ pages of open-source intelligence techniques for uncovering online information about people, organizations, and infrastructure.
Open Source Intelligence Techniques
Resources for searching and analyzing online information — social networks, search engines, archives, images, documents, and automating OSINT workflows.
Operator Handbook — Red Team Reference
Quick-reference red team field manual — Linux/Windows/Mac commands, network tools, exploitation one-liners, and operational cheat sheets for active engagements.
Penetration Testing Azure for Ethical Hackers
Azure penetration testing guide — Azure AD attacks, storage exploitation, function app abuse, managed identity attacks, and cloud privilege escalation chains.
Pentesting Azure Applications — The Definitive Guide
In-depth Azure application security testing — web apps, APIs, containers, service buses, Key Vault attacks, and full Azure attack surface enumeration.
Practical Cloud Security
Cloud security fundamentals and attack techniques — AWS, Azure, GCP security controls, IAM misconfigurations, network security groups, and container security.
Practical IoT Hacking
Definitive guide to attacking Internet of Things devices — firmware extraction, hardware debugging, radio protocols, MQTT attacks, and IoT network exploitation.
Practical Linux Forensics
Linux digital forensics guide — evidence collection, memory analysis, disk forensics, log analysis, malware artifact identification, and timeline reconstruction.
Practical Malware Analysis
Complete malware analysis guide — static and dynamic analysis, disassembly, debugging, unpacking, and reverse engineering real malware samples.
RTFM — Red Team Field Manual v2
The essential red team quick-reference — Windows/Linux commands, network tools, web exploitation, post-exploitation one-liners, and operational cheat sheets.
Red Team Development and Operations
Professional red team operations guide — engagement planning, C2 infrastructure, operational security, reporting, and running effective adversary simulations.
Reversing — Secrets of Reverse Engineering
Complete reverse engineering guide — x86/x64 assembly, disassemblers, debuggers, anti-reversing techniques, software cracking, and malware reversing.
Serious Cryptography
Practical cryptography for security professionals — block ciphers, hash functions, public key cryptography, TLS, random number generation, and cryptographic attacks.
The Android Malware Handbook
Android malware analysis and reverse engineering — APK analysis, smali code, dynamic analysis, evasion techniques, and real Android malware case studies.
The Art of Intrusion
Real hacker stories — the techniques, social engineering, and exploits used in famous break-ins told from the attacker's perspective by Kevin Mitnick.
The Art of Mac Malware
macOS malware analysis and reverse engineering — Mac-specific attack techniques, persistence mechanisms, code signing bypass, and analyzing real Mac malware.
The Car Hacker's Handbook
Automotive penetration testing guide — CAN bus attacks, OBD-II exploitation, ECU reverse engineering, wireless attacks on vehicles, and automotive security research.
The Hacker Playbook
Practical penetration testing guide structured like a football playbook — reconnaissance, scanning, exploitation, and post-exploitation plays with real-world scenarios.
The Pentester BluePrint — Starting a Career as an Ethical Hacker
Career guide for aspiring pentesters — skills, certifications, building a lab, getting hired, and navigating the ethical hacking industry.
The Shellcoder's Handbook
Discovering and exploiting security holes — buffer overflows, heap exploitation, format strings, return-oriented programming, and writing shellcode for multiple platforms.
The Social Engineer's Playbook
Practical pretexting guide — phishing scripts, vishing techniques, physical social engineering, building personas, and psychological manipulation tactics.
The Web Application Hacker's Handbook (2nd Edition)
The definitive web application security bible — finding and exploiting security flaws in modern web applications, covering all OWASP Top 10 and advanced techniques.
This Is How They Tell Me the World Ends — The Cyberweapons Arms Race
The untold story of the global cyberweapon trade — zero-days, nation-state hacking, surveillance tools, and the shadow market for digital weapons.
Tribe of Hackers — Red Team
Insights from top red team professionals — career advice, tools, methodologies, and mindset from the world's best offensive security practitioners.
Web Application Security
Modern web application security guide — XSS, CSRF, clickjacking, CSP, CORS misconfigurations, authentication attacks, and securing web applications.
Cyberjutsu — Cybersecurity for the Modern Ninja
Ancient warrior philosophy applied to cybersecurity — stealth, deception, situational awareness, and the mindset of a modern cyber warrior.